Organizations must build on existing security practices and embrace phishing-resistant authentication to deliver robust protection.
Similar Posts
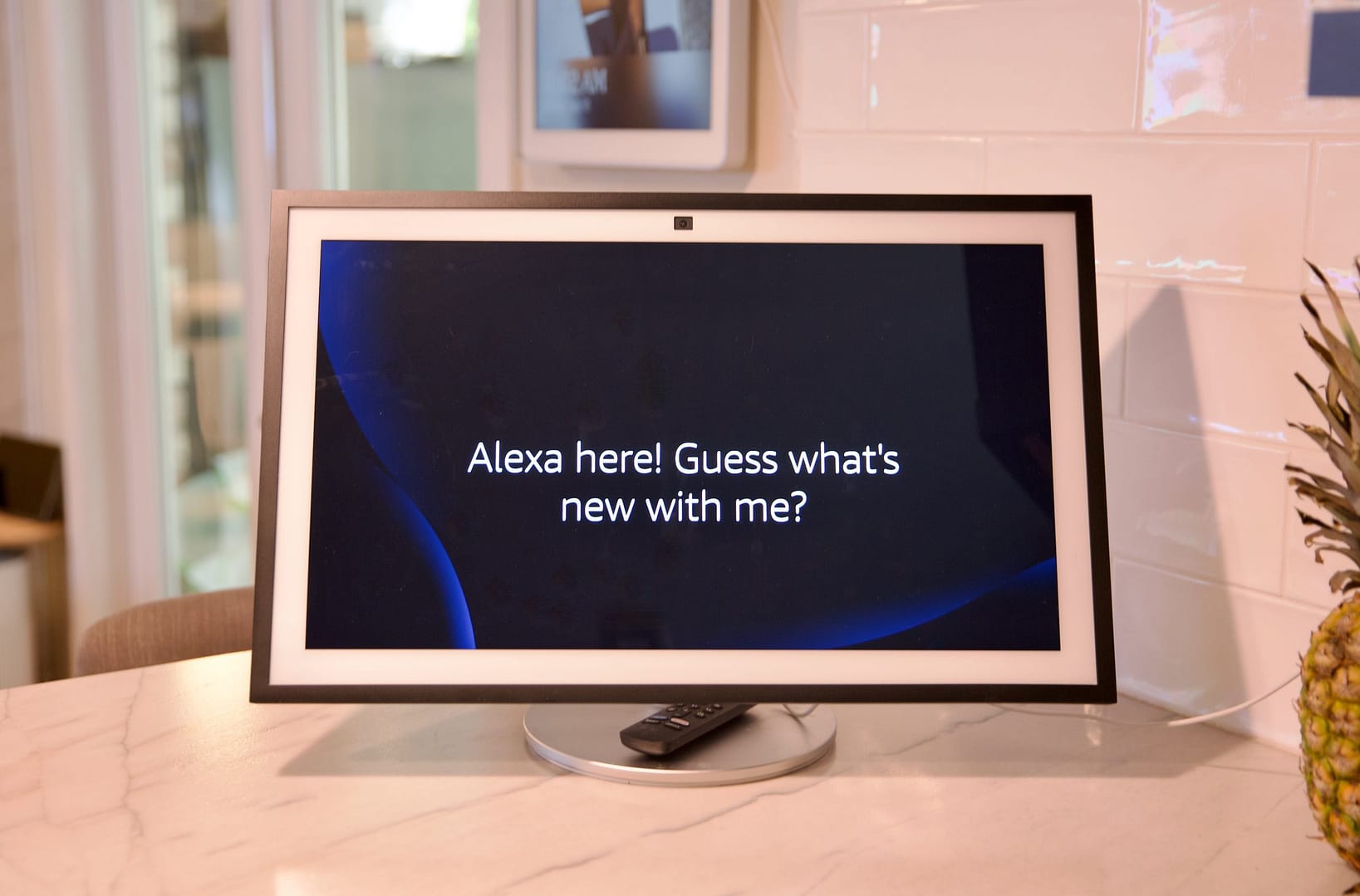
24 hours with Alexa Plus: we cooked, we chatted, and it kinda lied to me
BysgadminThere’s a new AI in the house. I’ve waited two years to try out the new Alexa, which was first announced…
The SSD version of LaCie’s iconic Rugged drive gets a speed boost
BysgadminThe new LaCie Rugged SSD4 is compatible with computers, tablets, and smartphones. | Image: Seagate Neil Poulton succeeded in elevating the…
I’ve hunted out the best Galaxy S26 cases to keep your swanky new phone protected
BysgadminSamsung Galaxy S26 is about to start shipping, so it’s time to get your case sorted now.
The second-gen AirTags are a scatterbrain’s best friend
BysgadminThe biggest con is this so-called Midnight Purple keyring is barely purple. It’s the iPhone 14 Pro Max Deep Purple all…
The ‘Epstein files’ implosion bleeds into foreign policy
BysgadminWhile the summer doldrums have hit Washington, the MAGA influencers can never truly go on vacation, especially if they’ve spent their…
What is the release date for Stranger Things season 5 part 2 on Netflix?
BysgadminHere’s when you can watch Stranger Things season 5’s next three episodes on Netflix.